IT Security Integration
CSI Process for Network Security Solutions :
Network Security Assessment
- Internal and external test using various attack techniques
- Authentication, Authorization and Accounting (AAA) review
- Router, Firewall, IDS, IPS rule-set, and configuration reviews
- Network, server, and infrastructure assessment
- Active and Passive analysis utilizing various scan technologies
- Analysis of information security policies and procedures
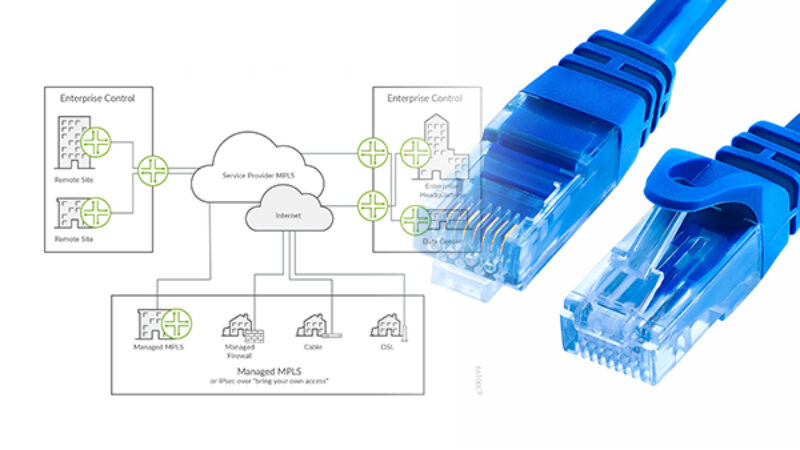
Computer and System Network Security Design
- Virtual Private Networks, and Remote Access architectures and topologies
- Intrusion Detection Systems and Intrusion Prevention Systems
- Firewall architectures, DMZ requirements, and redundancy
- Encryption, and Authentication recommendations
- Wireless Security 802.11x, PEAP, EAP
- Mail Cleanser, Content Filtering
- Anti-Virus, Anti-Spy ware
- SAN and IP encryption
Network Security Deployment
- Monitored and Managed Firewalls, IDS, and IPS
- Implementation of designed security solution
- Verification of deployed security solutions
- Operating system hardening
- IOS System hardening
- Patch Management
Continued Network Services
- Routine scans and vulnerabilities
- Log Reviews and GAP Analysis
- IDS, and IPS tweaking
- Patch Updates
- Documentation, and data archival for compliance requirements
Closed Circuit and Surveillance Monitoring System (CCTV)
- Reviews and GAP Analysis CCTV requirements
- Design and deploy CCTV system
- CCTV deployment on special environments or conditions
- CCTV integration with other Network and Security equipment